The belief that modern cloud security platforms can fully eliminate cyber risk is widespread. Managed services, automated protections, and globally distributed infrastructure often create a sense of security that feels complete.
The recent Cloudflare zero-day vulnerability, which enabled attackers to bypass certain protections, challenges that belief and reinforces a long-standing cybersecurity principle: defense in depth still matters.
This incident is not a failure of Cloudflare as a security provider. Cloudflare remains one of the most mature and security-focused companies on the internet. Instead, the incident highlights a broader lesson for organizations of all sizes. No single tool or platform can provide absolute security. Layered defenses remain essential, even in advanced cloud environments.
What the Cloudflare Zero-Day Revealed
A zero-day vulnerability is a security flaw that is unknown to the vendor or defenders and has no available fix at the time it is exploited. It can exist in software, hardware, firmware, operating systems, or system design, allowing attackers to take advantage of it before anyone has time to detect or patch it. In this case, the vulnerability allowed malicious actors to bypass some Cloudflare security protections, potentially exposing downstream applications.
Cloudflare services such as web application firewalls, DDoS mitigation, and bot protection are commonly used as the first line of defense. When a vulnerability affects a control that sits at the perimeter (the boundary where external traffic first interacts with internal systems, such as firewalls) of the internet, the impact can be widespread. Thousands of organizations rely on these protections to block attacks before they reach internal systems.
The key takeaway is not that vulnerabilities exist; it is a reality that is unavoidable in complex systems. The issue is the assumption that perimeter security alone is sufficient. When attackers bypass that perimeter, organizations without additional layers of defense are left exposed.
Why Defense in Depth Still Matters
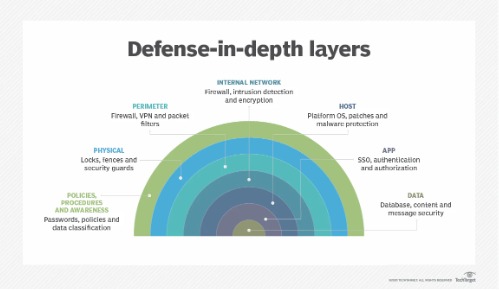
Defense in depth is a cybersecurity strategy that relies on multiple, overlapping security controls to provide comprehensive protection. If one layer fails, others continue to protect systems and limit damage. This approach assumes that breaches are inevitable and focuses on resilience rather than perfect prevention.
The Cloudflare zero-day illustrates why this philosophy remains critical. When perimeter defenses are bypassed, the next question becomes what stops the attacker. Without internal safeguards, attackers can move freely once they gain access to an application or service.
A strong defense-in-depth strategy typically includes network segmentation, application security, identity and access management, endpoint protection, monitoring, and incident response. Each layer addresses different attack techniques and reduces reliance on any single control.
The Risk of Over-Reliance on Cloud Security Providers
Cloud security providers offer powerful and scalable protections, but they do not replace internal security responsibilities. Over-reliance on a single vendor creates a concentration of risk. When that vendor experiences a vulnerability, misconfiguration, or outage, customers inherit the impact.
Many organizations adopt cloud security services, believing security is fully handled on their behalf. This mindset often leads to gaps such as weak authentication controls, excessive permissions, limited logging, and insufficient monitoring.
The Cloudflare incident reinforces the shared responsibility model. While providers secure their platforms, customers remain responsible for securing their applications, identities, and data. Defense in depth ensures this responsibility is addressed rather than assumed away.
Security Layers That Reduce Impact When Perimeters Fail
When a web application firewall is bypassed, other security controls should still limit attacker success. Strong identity and access management prevent unauthorized actions even if an application is reached. Least privilege access reduces the blast radius of compromised components.
Application-level protections such as input validation, rate limiting, and secure coding practices can stop or slow malicious requests. Runtime application self-protection and anomaly detection tools help identify behavior that perimeter defenses may miss.
Logging and observability are equally important. When attacks slip past edge protections, internal visibility determines how quickly they are detected and contained. Without logs and alerts, attackers can operate undetected for long periods.
Lessons for Security Teams and Enterprises
One of the most important lessons from this case is the need to design security architectures that assume failure. Even best-in-class controls can be bypassed. Planning for that reality leads to more resilient systems.
Security teams should regularly assess their dependence on external security services and ask critical questions. What happens if this control fails? What visibility is lost? How quickly would an incident be detected?
Threat modeling and tabletop exercises help organizations identify weaknesses beyond the perimeter. These exercises should include scenarios where trusted third-party security services are compromised or temporarily ineffective.
Continuous testing through penetration testing and red team exercises further supports defense in depth. These activities validate whether layered controls actually work together under real-world conditions.
Implications for Governments and Critical Infrastructure
For governments and operators of critical infrastructure, the consequences of security failures are amplified. Public services, healthcare systems, energy networks, and financial platforms increasingly rely on cloud-based security services.
The Cloudflare zero-day reinforces why national cybersecurity strategies emphasize resilience, redundancy, and layered defenses. Governments cannot rely solely on vendor assurances. Regulatory frameworks and procurement standards must require defense-in-depth architectures and continuous risk evaluation.
Investment in internal monitoring, skilled security teams, and incident response readiness remains essential. Defense in depth is not optional for critical systems. It is a strategic requirement.
Defense in Depth and Zero Trust Are Not Opposites
Some view zero-trust architectures as a replacement for traditional defense in depth. In practice, zero trust builds on the same principles. It assumes breach and enforces verification at every step.
The Cloudflare incident aligns closely with zero-trust thinking. When perimeter trust is broken, identity verification, device posture checks, and continuous monitoring become the next layers of defense. Without these controls, zero trust remains theoretical rather than practical.
Conclusion
The Cloudflare zero-day vulnerability is a timely reminder that no security control is infallible. Even trusted platforms can be bypassed. Organizations that depend on a single layer of protection expose themselves to unnecessary risk.
Defense in depth remains one of the most effective cybersecurity strategies available. By layering controls across networks, applications, identities, and monitoring systems, organizations reduce the impact of inevitable failures.
In a threat landscape shaped by zero-day vulnerabilities and sophisticated attackers, resilience matters more than perfection. Cloud security is powerful, but layered security is essential.