-
Event-Driven Cybercrime: How the Olympics Attract Scams

When the world watches the Olympics, cybercriminals move in. Discover how global sporting events fuel scams and how attackers exploit hype, urgency, and trust to strike at millions. The Cybersecurity Pattern Behind Major Global Events Large global events do more than gather spectators, sponsors, and media attention. They also attract cybercriminals. Security professionals refer to
-
Securing AI Agent Marketplaces: A Closer Look at OpenClaw’s VirusTotal Scanning
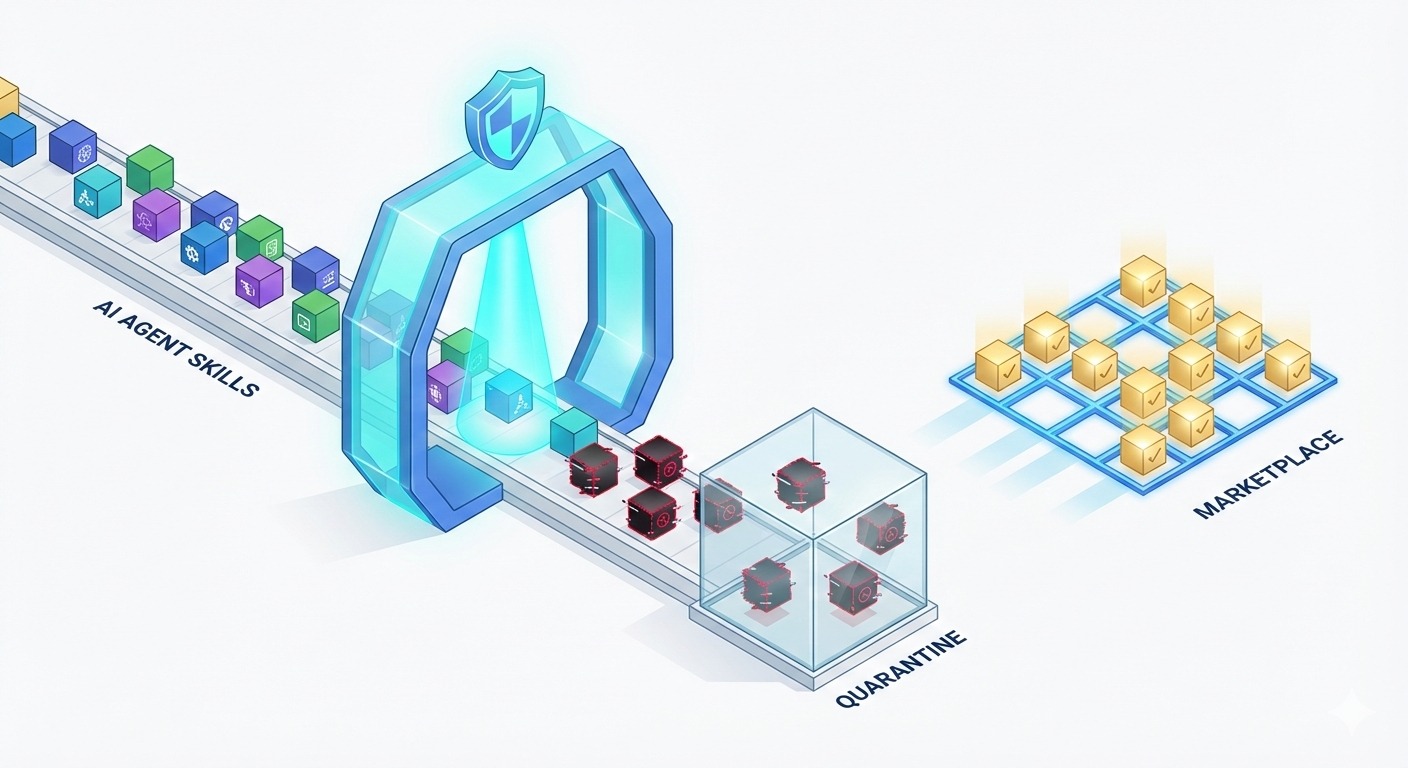
OpenClaw’s integration of VirusTotal scanning reveals a critical shift in AI agent marketplace security. Discover how malicious ClawHub skills are detected and why AI marketplaces are prime targets for abuse. The Growing Importance of AI Agent Marketplace Security An AI agent marketplace is a digital platform where developers publish and distribute skills, tools, or extensions
-
Defense in Depth Still Matters: Cloudflare’s Zero-Day as a case study

The belief that modern cloud security platforms can fully eliminate cyber risk is widespread. Managed services, automated protections, and globally distributed infrastructure often create a sense of security that feels complete. The recent Cloudflare zero-day vulnerability, which enabled attackers to bypass certain protections, challenges that belief and reinforces a long-standing cybersecurity principle: defense in depth
-
How a Security Hole in Moltbook Exposed Risks of AI-Driven Social Networks

Learn how a serious security hole in Moltbook revealed broader dangers in AI-driven social networks, the risks of autonomous systems, and best practices for securing them.
-
Why Governments Can No Longer Be Passive in Cybersecurity

Governments can no longer ignore cybersecurity risks. Learn why proactive cyber policy is now critical for national security and public trust. Cybersecurity is no longer an optional or peripheral concern for governments. In a world where public services, national infrastructure, and economic activities are deeply digital, states cannot afford to remain reactive or passive. The
-
From Victim to Vector: How Infostealer Malware Exploits Legitimate Business Websites

For a long time, we’ve thought about cyberattacks in fairly simple terms: attackers build malicious infrastructure, victims accidentally stumble into it, and damage follows. But that mental model is quietly breaking down. Today, many of the most effective malware campaigns, especially infostealer malware, no longer rely on obviously malicious websites. Instead, attackers are increasingly turning
Search
About
Secneedle provides practical cybersecurity guidance across compliance, training, and incident response readiness.
Archive
Categories
Recent Posts
Tags
Gallery